Table of Contents
- Overview
- Choosing a System
- Example Systems
- Network Cameras
- USB and Thunderbolt Devices
- Audio
- Remote Access
- Triggering Actions
- Getting Help
Overview
This manual is designed to help you create a complete CCTV system based around SecuritySpy, our macOS video surveillance software.
Three questions usually arise when setting up a new system:
Which cameras should I buy?
Start by reading the Choosing a System section, which describes the various choices of cameras and Mac models available.
What other equipment do I need?
Take a look at the Example Systems section, which describes the hardware you need for the most common system configurations. To read more about cameras, see the Network Cameras section.
How do I set up my system?
The sections Connecting to a Camera Over Ethernet and Connecting to a Camera Over WiFi guide you through the process of configuring IP cameras, and the Remote Access section shows you how to set up access to your system from the Internet.
For information about using the SecuritySpy software itself, see the SecuritySpy User Manual.
Choosing a System
Your main choices are which cameras to use, and which Mac computer, for your SecuritySpy video surveillance system.
Types of Camera
Network cameras
All new systems should use IP cameras (network cameras). These are digital devices that transmit high-definition video over Ethernet or wireless (WiFi) networks. IP cameras are designed for CCTV, and can offer high quality video, with additional features such as infra-red night vision, vandal resistance and Pan/Tilt/Zoom. Read more in the Network Cameras section of this manual.
Analog cameras
Previous-generation CCTV systems employed analog cameras, which transmit analog video signals over coaxial cable. Analog cameras provide very poor quality video by today's standards, and should not be used. Still, if you want to connect analog cameras to SecuritySpy, you can do so using Axis Video Encoders.
Webcams
The third type of camera is one connected by USB or Thunderbolt, or a built-in FaceTime camera (SecuritySpy calls these "local devices" to distinguish them from network devices). While these can make useful and inexpensive additions to CCTV systems, they have significant limitations: they are typically indoor-only, they have to be close to the Mac due to cable length restrictions, and connecting multiple devices can be tricky due to hardware and bandwidth restrictions. Therefore, if you do decide to use a local device, use just one of them, combined with one or more IP cameras. Read more in the USB and Thunderbolt Devices section of this manual.
Types of Mac
SecuritySpy will work on any Mac running macOS 10.13.6 "High Sierra" or later.
The amount of processing power required varies depending on a number of factors. Use our SecuritySpy System Requirements Calculator to help you choose a system to suit your Mac, or a Mac to suit your desired system.
By way of illustration, following is a rough guide to the maximum number of IP cameras of different Megapixel (MP) resolutions that you can connect to various Macs, assuming the cameras are providing H.265 video at 10 frames per second (FPS) that is being recorded by SecuritySpy directly to disk with no recompression:
 |
Mac mini (2024, Apple M4 processor, 10 cores)124 cameras at 2 MP | 102 cameras at 4 MP | 58 cameras at 8 MP Mac mini (2024, Apple M4 Pro processor, 12 cores)155 cameras at 2 MP | 132 cameras at 4 MP | 86 cameras at 8 MP The Mac mini is a particularly good choice to run SecuritySpy, due to its powerful CPU, GPU and neural engine, small size, and low cost. |
|
 |
Mac Studio (2025, Apple M4 Max, 14 cores)186 cameras at 2 MP | 158 cameras at 4 MP | 100 cameras at 8 MP Mac Studio (2025, Apple M3 Ultra, 32 cores)256 cameras at 2 MP | 256 cameras at 4 MP | 210 cameras at 8 MP |
|
 |
Mac Pro (2023, Apple M2 Ultra, 24 cores)256 cameras at 2 MP | 256 cameras at 4 MP | 210 cameras at 8 MP |
|
 |
iMac (2024, Apple M4 processor, 8 or 10 cores)124 cameras at 2 MP | 102 cameras at 4 MP | 58 cameras at 8 MP |
This list shows recent models, but older Macs, especially those with Apple Silicon chips, are very capable and can also work very well for SecuritySpy. In all cases, the maximum number of cameras varies depending on the video codec, frame rate, resolution, and available RAM. Use our System Requirements Calculator to obtain accurate estimates.
Modern IP cameras supply video in H.264 or H.265 format. Both are highly efficient codecs, with H.265 roughly twice as efficient (i.e. half the amount of storage space required).
Example Systems
The large range of available hardware options can be daunting when setting up a new system. For this reason, we've designed three comprehensive example systems that you can use as starting points for your own:
-
Home
A basic system using a standard Mac mini and inexpensive cameras to keep costs down while providing effective video surveillance.
-
Small to medium business
A flexible system using a Mac mini and high-resolution IP cameras, allowing for a high number of cameras and excellent quality.
-
Professional
Up to 210 high-end 8 MP cameras per Mac Studio for ultimate power and quality.
Example System - Home
 |
CamerasThere are many cameras on the market today that offer impressive quality at reasonable prices. For example, the Hikvision DS-2CD2446G2-I is a compact camera with a great feature set. 2 MP should be considered your minimum resolution requirement, although it's often not too much more expensive to purchase cameras with higher resolutions. Consider using PoE (Power-over-Ethernet) cameras for reliability and easy setup. |
 |
Ethernet switchUse a Gigabit-speed switch and connect all cameras by wired Ethernet where possible, for maximum performance and reliability. If necessary, a few WiFi cameras can also be used, which requires a wireless router or access point. |
 |
CablingUse Cat-5e Ethernet cables to connect everything to the switch. |
 |
StorageAllow 15 GB of storage space per 2 MP H.265 camera per month (double for H.264), and use an external SSD or HDD connected by USB 3.0, USB 3.1, or Thunderbolt. |
 |
Mac miniA basic M4 Mac mini with 16 GB RAM is the best choice for a home system, as it provides more than enough power, as well as great value. |
Example System - Business
 |
CamerasThe Hikvision compact camera shown above is a great choice for an indoor business environment too. Alternatively, consider the Axis M3086-V, an indoor mini-dome, or the Hanwha Techwin QNV-8080R, an outdoor dome. The Vivotek IB9380-HV-V2 is a good choice for an outdoor bullet camera. 4 MP should be considered your minimum resolution requirement. PoE (Power-over-Ethernet) cameras are highly recommended for ease of setup and reliability. |
 |
Ethernet switchUse a Gigabit-speed PoE switch, and connect all devices to this switch. |
 |
CablingUse Cat-5e cabling for the cameras, and Cat-6 or Cat-7 cabling for the rest of your network to future-proof it for 10-Gigabit speeds. |
 |
StorageAllow 30 GB of storage space per 4 MP H.265 camera per month (double for H.264), and use an external SSD or HDD connected by USB 3.0, USB 3.1, or Thunderbolt. |
 |
Mac miniA basic M4 Mac mini with 16 GB RAM is usually more than powerful enough to manage a medium-sized business installation. For larger systems, consider the upgraded M4 Pro model. |
Example System - Professional
 |
CamerasAxis, Vivotek, Hikvision and Dahua make some excellent high-resolution cameras in various form factors, for example the AXIS M4218-V or the Vivotek IT9399-HVW. The Dahua IPC-PDW5849 is an impressive extra-wide camera with two 4 MP sensors that cover a 180° field of view. 8 MP should be considered your minimum resolution requirement. Make sure to use PoE (Power-over-Ethernet) cameras. |
 |
Ethernet switchUse a Gigabit-speed PoE switch to connect and power all the cameras. For the rest of your network, you might choose to use 10-Gigabit speed switches. |
 |
CablingUse Cat-5e cabling for the cameras, and Cat-6 or Cat-7 cabling for the rest of your network to allow for 10-Gigabit speeds. |
 |
StorageAllow 60 GB of storage space per 8 MP H.265 camera per month (double for H.264), and use an external RAID array connected by USB 3.1 or Thunderbolt. |
 |
MacA Mac Studio is ideal for large professional systems. A Mac Pro would also be suitable; compared with the Mac Studio it is more expandable, but also physically larger and more expensive. |
Network Cameras
Network cameras - also known as IP cameras - send digital video and audio data over an Ethernet or wireless (WiFi) network. They can be accessed by a computer on your local network or over the Internet without requiring any additional video input hardware.

SecuritySpy supports an extensive range of IP cameras - see the SecuritySpy Camera List to check compatibility and find a camera to suit your requirements. For specific recommendations, see our regularly-updated Camera Picks page.
Network Hardware
A network is typically composed of the following hardware components:
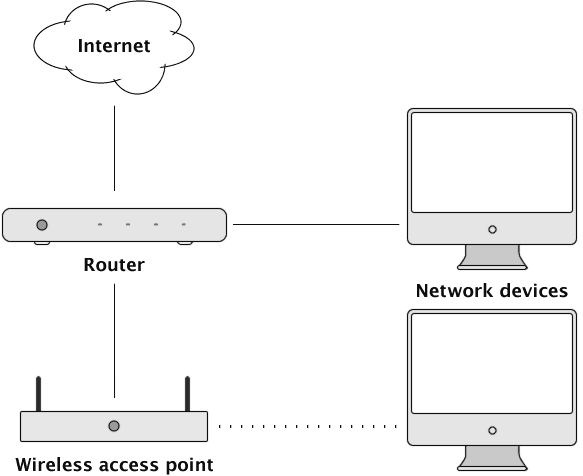
Router
There are actually two separate networks shown on the above diagram: the local network, consisting of all the devices pictured; and the Internet. The router acts as the link between the two, providing all the devices on the local network with Internet access.
Most routers have a built-in switch, providing multiple Ethernet ports. This may be sufficient for small networks, but for larger more demanding applications a separate switch is normally required to provide fast connectivity between more devices than can be supported by the router alone.

For example, this router has four LAN (Local Area Network) ethernet ports that you can use to connect devices. If the number of LAN ports on the router is insufficient, connect a switch to one of the router LAN ports, and connect all other devices into the switch. Good brands of switch include TP-Link, Ubiquiti and Netgear:

Wireless access point (WAP)
These devices add wireless capability to the local network. They bridge the wired and wireless sections of the network, connecting all devices together on the same network.
Some WiFi access points, especially mesh systems, are routers in themselves. If added to a network that already has a router (such as the one provided by your ISP), the second router creates a separate sub-network behind it. Devices on one sub-network cannot easily discover or communicate with devices on the other, which can cause a range of problems: printers and NAS drives may not be visible, casting and AirPlay may fail, smart home devices may become unresponsive, and VPN or gaming connections may behave unpredictably. Two routers can also mean two competing DHCP servers, leading to IP address conflicts and intermittent connectivity.
To avoid these issues, such devices must be set to "bridge mode" (sometimes called "access point mode"). This disables the device's routing functions so that it acts purely as a wireless access point, keeping all devices on a single network managed by your primary router.
Many routers have wireless functionality built in, so there is no need for a separate WAP.
Network devices
These are the devices that connect to the local network, either wired or wirelessly. Each device can communicate directly with any other device on the same local network, but in order to communicate with any device over the Internet, it must do this through the router.
Ethernet Cabling
For connecting cameras, Cat-5e Ethernet cable is suitable - it is inexpensive, widely available and allows for Gigabit speeds. For the rest of your network, you may want to use higher-spec Cat-6 or Cat-7 cable, to allow for 10-Gigabit speeds.

Power-over-Ethernet (PoE)
PoE eliminates the need for power connections at each camera location, which makes installing IP cameras much easier. There are different PoE standards that vary based on power level - make sure your switch is able to supply the level needed by your cameras (802.3af for standard PoE, 802.3at for PoE+, or 802.3bt for PoE++).
Local Networks
This section is an introduction to the concepts involved in understanding addresses on a LAN (Local Area Network).
IP address
Each device connected to a network is given a unique identifier, known as an IP address. An IP address consists of four numbers separated by dots, for example:
10.0.1.1
192.168.1.100
172.16.0.57
Port
When network devices send messages to each other, they do so on a particular port, which can be thought of as a particular communication channel. By using different ports, several services (e.g. web, email, file transfer) can operate independently on the same device.
By convention, port 80 is used to send and receive web pages (HTTP) and port 554 is used to send and receive video and audio media streams (RTSP).
Subnet
Every LAN operates on a particular subnet, which defines the scope of the network; a device can directly communicate only with other devices on the same subnet.
The subnet is usually indicated by the first three numbers of the IP address, leaving the fourth number to identify the devices themselves. The following IP addresses are all on the same subnet:
10.0.1.1
10.0.1.2
10.0.1.163
This arrangement is described by the subnet mask "255.255.255.0", which means "use the first three numbers as the subnet, and use the fourth number as the device identifier".
Refer to the Network pane of the System Settings to identify which subnet addressing is being used on your LAN.
DHCP
DHCP is a protocol, built into all routers, that automatically assigns IP addresses to devices on the LAN. This makes it easy to connect a device to a network, however it means that device addresses may change from time to time. This is often unsuitable for any device that acts as a server (e.g. a network camera), because servers must have fixed addresses so that clients know where to find them.
So, you may need to give your cameras static IP addresses on your LAN - see the Connecting to a Camera Over Ethernet section below.
Note that any manual address you assign to a device should be outside the range of addresses that the router uses for DHCP, to avoid any conflict. Routers vary in what ranges they use, but if you assign manual addresses in the range 200-250, this is normally safe. It's a good idea to look for this setting in your router so that you know which addresses are safe to use for your manual assignments.
Connecting to a Camera Over Ethernet
This section explains how to set up network cameras on your local network, to be accessed by SecuritySpy running on the same network. If, instead, you want to make your cameras directly available over the internet (most users will not need to do this), also see Remote Access - Introduction and Port Forwarding - Manual Setup.
Methods 1 and 2 described below rely on the camera being able to obtain an IP address automatically using DHCP. Fortunately, most cameras are pre-configured to do so, and most networks contain a DHCP service (typically provided by the router). If your camera does not use DHCP, or if your network does not have a router, then you will need to use method 3.
1. ONVIF cameras, or cameras that support Bonjour (Zero Configuration Networking)
For cameras that support either of these protocols, setup is straightforward. Simply connect the camera to your network, and in the Settings -> Cameras -> Device section in SecuritySpy, create a new network device, click the Auto-Discovered Devices button, and select the camera from the list. There is no need to interact directly with the camera's IP address.
In terms of authentication, most ONVIF cameras have one set of usernames/passwords that can access both the camera's web interface as well as the ONVIF video streams. However, a minority of cameras have a separate, independent set of ONVIF users, so if you receive authentication errors after entering the same login details used to access the camera's web interface, this is something to check for via the camera's settings pages.
2. Cameras with a DHCP address by default
For cameras that use DHCP, but do not support ONVIF or Bonjour, you'll initially need to locate the camera on your network, and then assign it to a static IP address.
To help you find the IP addresses assigned to your cameras, use our Network Device Finder utility, which lists the IP addresses of all web servers on your local network:

- Click the Start button (the Port setting should normally be set to 80, though many Foscam cameras use 88 instead).
- When the camera is found and added to the list, double-click on it to open it in a web browser.
- Assign the camera to a manual IP address on the same subnet as the rest of the network. Make sure this address is not being used by any other device, and that it is outside the range reserved for DHCP by your router (see the Local Networks section of this manual for more information).
- For the Subnet Mask setting, you should typically specify 255.255.255.0.
- You may need to restart the camera for the changes to take effect.
For example, if your network uses the subnet 192.168.1 (i.e. all devices on your network have IP addresses in the form 192.168.1.x), and your router uses the range 192.168.1.50 - 192.168.1.200 for its DHCP assignments, then you can use addresses 192.168.1.201, 192.168.1.202, 192.168.1.203 etc. for your cameras.
3. Cameras with a fixed address by default
First, determine whether the camera is on the same subnet as your Mac. Open Terminal (you'll find it in your /Applications/Utilities/ folder), and enter the following command:
route get default
Look for these two lines in the output (you may see different values):
gateway: 192.168.1.1
interface: en0
Compare the first three numbers of the gateway IP address with the camera IP address: if they match, they are on the same subnet and the camera can be accessed directly. If they don't match, issue the following additional command:
sudo ifconfig NAME alias A.B.C.D 255.255.255.0
where NAME is the interface name (e.g. en0), A.B.C are the first three numbers of the camera IP, and D is a number that is different from the camera IP. For example, if the camera IP is 10.0.0.1, your command could be:
sudo ifconfig en0 alias 10.0.0.2 255.255.255.0
You should then be able to connect to the camera at its static IP address.
Connect to the camera in Safari, locate its network settings, and change it to DHCP, or to a static IP that is compatible with your network (i.e. where the first three numbers match the gateway address, and the final number is unique to the camera and not used by any other device).
Connecting to a Camera Over WiFi
Initially, you will need to connect the camera to your switch or router using an Ethernet cable, and follow the above instructions, Connecting to a Camera Over Ethernet.
Once connected by Ethernet, use a web browser (e.g. Safari) to open the camera's settings pages, and locate the camera's WiFi settings. Here you will need to enter the information required to establish a wireless connection: typically the network name (SSID) and password. If you have to choose an encryption type, this is typically WPA2 or WPA3, however you should confirm this by checking the WiFi encryption settings in your wireless router or access point.
If the camera does not support Zero Configuration Networking (see method 1 in the above section), you may need to manually assign an IP address to the camera's WiFi interface, just like you did with its Ethernet interface.
Recommended Camera Settings
There are a few other settings available in most IP cameras that you should check:
Video stream frame rate
You should set the frame rate of the camera's video stream to the lowest rate that is acceptable for your purposes. Frame rates that are too high waste network bandwidth and your Mac's CPU resources. A frame rate of 5-10 is typically sufficient for general-purpose video surveillance.
Video stream key frame rate
H.264 and H.265 streams comprise key frames (I-frames) each followed by multiple delta frames (P-frames). The delta frames encode only the changes in the image since the previous frame. The key frame rate — sometimes called "I-Frame Rate", "Key Frame Interval", "GOV Length" or "Intra Frame Period" — determines how frequently key frames appear in the video stream (e.g. a key frame rate of 10 means that each key frame is followed by 10 delta frames).
Don't set the key frame rate too high. Beyond around 30, the bandwidth improvements are minimal, and streams with higher key frame rates are more difficult to process (resulting in more memory and CPU usage). Also, using a low key frame rate means that any corruption in the video stream (e.g. due to temporary network difficulties) will be short-lived.
The ideal setting is to have a key frame every 2-3 seconds or so. For example, if the video stream frame rate is 10, then a good key frame rate to use is around 20-30.
Video bit rate
Many cameras offer the choice between VBR (Variable Bit Rate) and CBR (Constant Bit Rate) video encoding. Choose VBR with a medium-to-high quality setting — this allows the camera to adjust its bit rate to cope with different conditions (e.g. if there is lots of movement the camera will increase its bit rate in order to encode it accurately). If only CBR is available, then make sure to use a bit rate towards the higher end of the camera's available range, to ensure good quality across all conditions.
Date overlay and time server
Most cameras have the ability to add a date and time stamp onto the video image, and if so, you will probably want to enable this feature.
Most cameras also allow you to specify an NTP (Network Time Protocol) Server, that the camera can use to automatically maintain the correct date and time. For this you can specify time.apple.com.
Note that for this to work, the camera's IP settings need to include the router address (this can be obtained from the Network system settings on your Mac) and a DNS server address (you can use 8.8.8.8, which is the address of Google's free DNS server).
Audio stream format
If the camera supports AAC encoding, then you should use this, as it is a very efficient format that offers good quality.
USB and Thunderbolt Devices
SecuritySpy supports USB, Thunderbolt and built-in video devices (which it refers to as "local" devices, to distinguish them from network devices). Such devices typically are not suitable for video surveillance, but can be a useful addition to a CCTV system in certain circumstances, and can be useful when using SecuritySpy for non-CCTV purposes (e.g. recording scientific experiments).
USB cameras
Often referred to as "webcams", these are small cameras that connect to your Mac via a USB cable. SecuritySpy supports any camera that implements the "UVC" protocol using driver software that is built into macOS, though non-UVC cameras that use driver software supplied by the manufacturer may also work.

Adding one of these into the mix of cameras in a CCTV system is inexpensive and easy, and can make a useful addition (e.g. for covering the room containing the recording Mac). However, USB cameras suffer from significant limitations:
- The optics are generally low-quality, and casings are not designed for permanent mounting.
- USB has a limited cable length, so the cameras will need to stay close to the Mac.
- USB cameras provide uncompressed video, which has to be encoded by SecuritySpy for recording, using significant processor time.
- Connecting multiple devices is problematic: one USB-2.0 camera will use all available USB bandwidth, so you will be limited to a single USB-2.0 camera. This is not such a problem with USB-3.0 devices, though physically connecting multiple devices can be a problem.
Built-in cameras
Built-in FaceTime cameras will work with SecuritySpy.
Blackmagic devices
SecuritySpy supports Blackmagic video input devices. Blackmagic produce an array of high-quality video devices, from cinematic cameras that connect to your Mac by Thunderbolt, to HDMI and SDI video input devices that connect to your Mac by USB or Thunderbolt.

These devices are not generally designed for video surveillance, but are exceptionally high quality and can be used either for CCTV or other purposes.
Audio
SecuritySpy can monitor and record audio alongside the video from your cameras. SecuritySpy can access audio directly from network cameras, and in addition, you can connect one or more microphones to your Mac, with each one assigned to any number of cameras.
USB and Thunderbolt
There are many inexpensive USB audio input devices available that provide two inputs (stereo). There are also larger devices, generally designed for studio audio recording, with more than two inputs. Any audio input device that advertises Mac compatibility should work with SecuritySpy.
Audio from IP Cameras
Many audio-enabled IP cameras have a built-in microphone, but others have an audio input port to which you will need to connect a separate microphone:

These devices typically require 12-volt power, and supply a line-level mono audio signal.
Two-way audio
SecuritySpy supports two-way audio for IP cameras, whereby you can speak into a microphone connected to your Mac, and SecuritySpy will send this to the camera to play back via its speakers. Axis, Dahua Technology, Amcrest and Hikvision cameras are supported for computer-to-camera audio, as well as any camera that supports the open ONVIF standard.
Remote Access
SecuritySpy's built-in secure web server allows you to monitor your system over your local network or over the Internet from a remote location.
You can access SecuritySpy's web interface from any desktop web browser on another Mac or PC computer. Additionally, we have mobile apps for iOS, tvOS and Android, which allow you to easily access SecuritySpy from your phone, tablet or TV.
When accessing your system using a web browser, you can view live and recorded footage, control cameras with pan/tilt/zoom support, and modify SecuritySpy's settings.
You can set up multiple user accounts, each with varying levels of permissions, giving you control over who can access which features of your SecuritySpy server.

Caveat
Most Internet connections provide a true public IP address, and this is what the below instructions assume. However, some connections - most notably cellular and satellite connections - do not: instead, they employ what is known as Carrier-Grade NAT, which gives you an IP address on their own internal network that cannot accept incoming connections from the Internet. In this case, refer to our article Remote Access Without Port Forwarding for solutions.
Introduction
Addresses of devices on your local network are not directly accessible from the Internet. These addresses are private, and invisible from outside your local network (LAN).
Your local network is a LAN (Local Area Network), while the Internet is a WAN (Wide Area Network).
Your router, as the only device connected to both the LAN and the WAN, acts as a gateway between these two networks. When a device on the LAN needs to connect to a device on the WAN, it must do so via the router. Conversely, when a connection arrives from the WAN, the router is responsible for forwarding this to the appropriate device on the LAN - this is called port forwarding.

Your ISP (Internet Service Provider) provides you with a single public IP address. This address is part of the Internet. ISPs provide either a static or a dynamic public IP address:
Dynamic - most ISPs give you a dynamic IP address, which means that it can change from time to time. In this case, you will need to use a Dynamic DNS (DDNS) service to provide your system with a static host name that will always point to your public IP address, even when it changes. SecuritySpy has a built-in DDNS system, described below.
Static - this means that your public IP address never changes. This is ideal, as it means that you can always access your system using the same address, however you still may want to set up a DDNS address, as it is easier to remember than an IP address.
Setting up Remote Access
Connect your Mac by Ethernet if possible
Wired Ethernet provides much better performance and reliability than WiFi. If possible, connect your Mac by Ethernet into your router or Ethernet switch. Once you have done this, turn off the Mac's WiFi connection, since it is no longer needed.
Add SecuritySpy to your firewall
On older macOS versions, this option is at System Settings > Security > Privacy, while on newer systems this is at System Settings > Network > Firewall. If the firewall feature is turned off, you don't need to do anything here. If the firewall is on, you need to either turn it off, or configure it to allow incoming connections to SecuritySpy. Click the Firewall Options button and drag the SecuritySpy application into the list.

Enable SecuritySpy's web server
Go to the Web section of SecuritySpy's Settings window:

Under Enable web server, enable both the HTTP (standard) and HTTPS (encrypted) options. HTTP is suitable for local network communication, however you should use HTTPS for remote access, to ensure your data cannot be intercepted and decoded.
HTTPS requires the use of a certificate in order to identify the server. When you create a DDNS address, SecuritySpy will create a certificate for this automatically. This simple solution will be ideal for the majority of users, but if instead you want to supply your own certificate, see the HTTPS Keys and Certificates section of the SecuritySpy User Manual.
Create a DDNS address
Enter a name of your choosing into the Dynamic DNS name box in the above window and press the Test button, and SecuritySpy will set up a DDNS address for you: in this example, the Internet address example.viewcam.me will point to your public IP address, and will be automatically updated whenever your public IP changes.
Port forwarding
When an incoming connection arrives from the Internet, your router needs to know which device on the local network to forward the connection to. Most users will be able to set this up in just a few clicks, using the Automatic Setup instructions below, however if your router does not support NAT Port Mapping Protocol (NAT-PMP) or Universal Plug and Play (UPnP), you'll need to follow the Manual Setup instructions instead.
Important: for security, forward only the secure HTTPS port, not the standard HTTP port, so that all data transferred over the Internet is encrypted.
Port Forwarding - Automatic Setup
Most routers support NAT Port Mapping Protocol (NAT-PMP) or Universal Plug and Play (UPnP), either of which allows automatic configuration of routers to allow incoming connections from the Internet. All you need to do is enable the Auto-configure router for HTTPS Internet access option in the above window and click the Save button. Then, you will be able to access SecuritySpy from the internet using an address like this:
https://example.viewcam.me:8001
This is an example address that is based on the above screenshot — to find out what addresses to use in your case, click the Access Info button in the above window.
If this doesn't work initially, verify that your router's NAT-PMP / UPnP option is enabled. If this doesn't solve the problem, follow the instructions below to set up port forwarding manually.
Port Forwarding - Manual Setup
This section describes how to manually set up port forwarding, for when your router does not support NAT-PMP or UPnP. If you have not already done so, first read the Network Hardware and Local Networks sections of this manual in order to familiarise yourself with the concepts involved.
The basic idea is to assign a specific local network IP address to your Mac, then to configure your router to forward incoming connections from the Internet to your Mac at this address.
Determine your Mac's current network details
Click the Access Info button under Settings > Web, and the following panel will be shown:

The relevant details here are the Mac's name, IP address, router address and MAC address, which are shown at the bottom of this panel. These items are used in the below configuration. If you see both Ethernet and WiFi details here, use the Ethernet details.
Log in to your router
Open a web browser (e.g. Safari) and enter the router's IP address; its login screen should appear. Log in using the username and password printed on the back of the router. If the web interface won't load, the router may instead require configuration via a mobile app provided by the manufacturer.
DHCP reservation
The next step is to reserve a fixed IP address for your Mac on the local network. Locate this function in your router, and add an entry for your Mac. Typically, this involves specifying the following items:
- MAC address. Sometimes the router will offer a list of devices to choose from - in such a list, you should be able to identify your Mac via its MAC address or its name.
- IP address - enter the IP address that is currently assigned to the Mac.
Note: other names for this function include "address reservation", "IP reservation", "static lease", "static IP assignment", and "fixed IP assignment".
As an alternative, you could configure your Mac with a static IP address via System Settings > Network, however a DHCP reservation is usually the easier option.
Port forwarding
Locate this function in your router, and add an entry for your Mac. Typically, this involves specifying the following items:
- Rule name: "SecuritySpy"
- Private / LAN IP address: enter the IP address of the Mac
- Public / WAN IP address: leave this blank
- Private / LAN port: 8001 (or the range 8001-8001 if a range is required)
- Public / WAN port: 8001 (or the range 8001-8001 if a range is required)
- Protocol: TCP
Note: other names for this function include "virtual server", "port mapping", "NAT forwarding", and "application sharing". Here are some examples of what this setting could look like:


If you are having trouble working out how to set this up for your particular router, the helpful portforward.com website provides setup guides for most routers, so should be able to guide you.
Accessing from the Internet
Once you have set up your DDNS name and configured your router's port forwarding settings, you will be able to access your SecuritySpy server from the Internet using an address like this:
https://example.viewcam.me:8001
Note that these public addresses may not work from within your network (this requires "loopback" in the router, which is not universally supported). To access your SecuritySpy server from within your network, use your Mac's LAN IP address or ".local" hostname instead.
Triggering Actions
You can set SecuritySpy to perform a range of actions in response to motion detection.
These actions include playing an alarm sound, sending an email containing still images, and launching an application or AppleScript.

Home
Use our HomeHelper app to link your SecuritySpy CCTV system with Apple Home or Home Assistant: for example, turn on a light when motion is detected in a camera, or trigger a camera to record if a Home PIR sensor detects movement.
Using the Cynical SecuritySpy plugin, SecuritySpy integrates with the Indigo home automation application based on the X10 and INSTEON standards. You can trigger actions in your home in response to motion detected by SecuritySpy (no scripting required), or get SecuritySpy to record in response to an event detected by Indigo (using AppleScript).

We also offer iOS and Android mobile apps, allowing you to receive notifications to your phone or tablet when motion is detected.
Getting Help
To find out how to use the SecuritySpy software itself, see the SecuritySpy User Manual.
You may also find an answer to your question on the SecuritySpy Online Help pages.
If you still have unanswered questions, please email us at support@bensoftware.com.